Payment Card Industry (PCI) compliance refers to the data security standards that businesses must adhere to if they capture, process, transmit, or store credit or debit card information. Also known as the Payment Card Industry Data Security Standard (PCI DSS), these guidelines are created and enforced by the PCI Security Standards Council (PCI SSC).
Properly protecting your business from security breaches potentially saves you tens of thousands of dollars or more in lost income.
In this PCI compliance guide:
- What is PCI compliance? The basics
- What does it cost to be PCI compliant?
- Demystifying PCI DSS compliance and PCI PTS certification
- Consequences of PCI non-compliance
- Making sure your small business is PCI-compliant
- Conclusion
What is PCI compliance? The basics
As credit card usage expanded around the turn of the century, each major card brand (Visa, Mastercard, Discover, and American Express) developed their own systems for protecting against fraud. Soon, however, these card brands united to create an industry-wide standard for protection, called the PCI DSS. The first iteration was launched in 2004 and has undergone many revisions to stay current. The most recent version (4.0) was launched on March 31, 2022.
To establish and maintain PCI compliance, there are 12 basic requirements every business needs to meet. Below is an excerpt from the official Requirements and Security Assessment Procedures, which you can find on the PCI website.
PCI DSS version 4.0
Goal 1: Build and maintain a secure network and systems.
- Requirement 1: Install and maintain network security controls to help protect cardholder data.
- Requirement 2: Apply secure configurations to all components in your card processing environment.
Goal 2: Protect account data.
- Requirement 3: Protect stored cardholder account data.
- Requirement 4: Encrypt transmission of cardholder data across open, public networks.
Goal 3: Maintain a vulnerability management program.
- Requirement 5: Protect all systems and networks against malware, and regularly update anti-virus software or programs.
- Requirement 6: Develop and maintain secure systems and software.
Goal 4: Implement strong access control measures.
- Requirement 7: Restrict access to cardholder data and system components by business’ need to know.
- Requirement 8: Identify users and authenticate access to system components.
- Requirement 9: Restrict physical access to cardholder data.
Goal 5: Regularly monitor and test networks.
- Requirement 10: Track and monitor all access to network systems and cardholder data.
- Requirement 11: Regularly test security systems and processes.
Goal 6: Maintain an information security policy.
- Requirement 12: Maintain a policy that addresses information security for all personnel.
PCI DSS v4.0 changes
PCI DSS 4.0 exists for the same reason as previous iterations – i.e., to continue to address emerging threats and technologies and to help safeguard sensitive payment data. How it achieves this, however, differs slightly from earlier data security standards.
Below are some high-level explanations of some of the changes to the latest PCI compliance updates.
- Industry-wide security methods must constantly evolve in order to keep pace with emerging threats within the payments landscape.
- PCI compliance is a continuous process instead of an end goal. This means organizations must constantly incorporate the latest best practices in order to keep payment data safe from thieves and hackers. Keep up with evolving trends by visiting the PCI Security Standards website.
- Previous versions of PCI DSS used relatively strict guidelines for maintaining security. Under version 4.0 however, organizations have more clarification on intent and purpose that may help make it easier to understand what the correct compliance response should be.
Note, however, that version PCI DSS 3.2.1 is still in effect and will retire starting March 31, 2024. There are some future dated requirements that are best practice until enforceable starting March 31, 2025.
What does it cost to be PCI compliant?
Becoming (and remaining) PCI compliant carries a range of costs. What you can expect to pay depends on your merchant level, which is dependent on variables such as:
- The size, location, and nature of your organization
- The number of card-based transactions you process annually
- How you capture and process card-based payments (i.e., in-person or online)
There may be additional costs associated with employee training, for example, which is voluntary for smaller organizations, but often required for larger ones. Upgrading magstripe POS terminals with more secure EMV-enabled readers also carries expenses. The same is true for eCommerce merchants that protect their visitors by adding Secure Sockets Layer (SSL) certificates to their sites. Of course, there are direct PCI compliance fees – normally calculated and charged by your payment processor.
These variables make it difficult to provide an exact “cost” for PCI compliance. However, smaller organizations can expect to pay $300 to $500 annually to become and remain compliant. By contrast, a multinational enterprise might need to spend $70,000 to $100,000 a year to remain in good standing.
However, the real costs come from non-compliance. Even if fraud never occurs in your organization, failure to meet the data security guidelines could result in penalties ranging from $5,000 to $100,000 – per month – until the issues have been fixed. If fraud happens, you may have to cover financial losses. Data breaches can often lead to expensive legal battles and investigations – not to mention diminished consumer confidence and fewer sales.
Demystifying PCI DSS compliance and PCI PTS certification
Now that you know the goals and requirements of PCI DSS, what should you do with that knowledge? Your business will be assessed against these security guidelines whether you like it or not. So, it’s best to understand how it can impact your day-to-day tasks and responsibilities.
Using PCI PTS certified devices
If you’re using a point-of-sale device (POS) that’s more than a few years old, chances are it’s not protecting you against potential threats in adherence to current security standards.
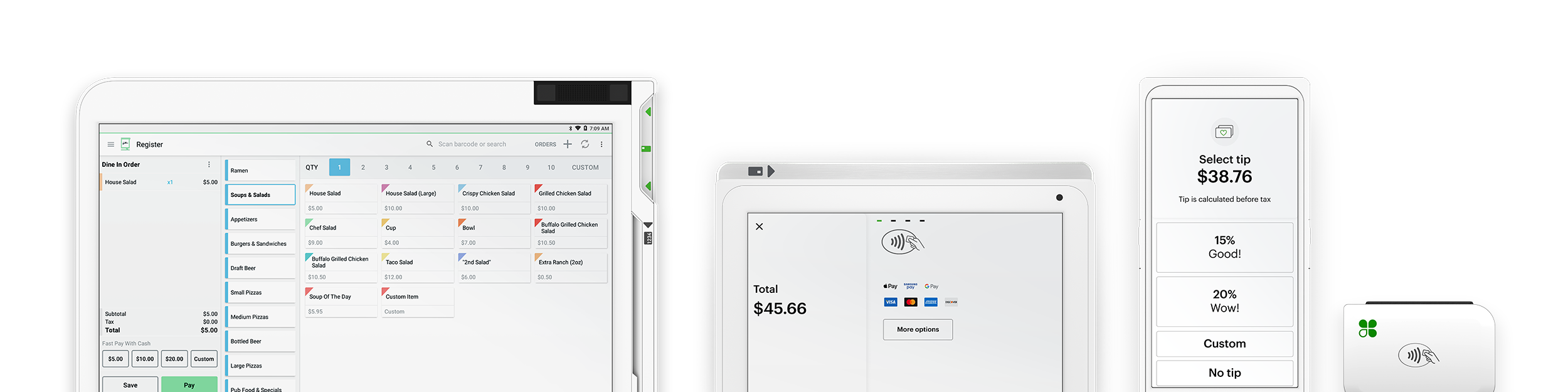
One way to simplify your security is to start with a modern POS, specifically one that is PCI PTS (Payment Card Industry PIN Transaction Security) certified. Think of PTS certification like PCI compliance for payment terminals. POS providers like Clover that provide payment terminals can submit their machines for inspection and certification to make sure that a third party will not be able to access cardholder and PIN information.
All Clover point-of-sale devices are PTS certified, taking much of the burden of PCI compliance off of busy merchants. One of the critical points of PTS certification is point-to-point encryption (P2PE). Having built-in P2PE, as merchants with current Clover POS systems do, will make the entire process of certifying PCI compliance much easier.
Avoiding hidden costs
If you cobble together your own payments processing, or use non-P2PE devices, you can hire outside PCI compliance consultants to survey your business and adapt your systems to meet the basic requirements. It may seem like avoiding a modern POS system will reduce costs, but when you’re planning your budget, be sure to factor in the cost of compliance consultants. It can quickly add up.
Assessing and reporting your PCI compliance
PCI compliance is assessed in two ways: Self-Assessment Questionnaires (SAQs) and audits. Generally, businesses are required to submit SAQs annually and are audited quarterly to ensure compliance.
Answering a questionnaire once a year many not sound that complicated, but how your business is structured and the number of credit card transactions you process dictate which of the 8 different SAQs you will have to complete.
What might initially seem like a simple checklist of requirements can balloon into over 200 questions examining things like your networks, login systems, and data storage. Here are a few items from the full questionnaire for merchants who aren’t P2PE certified:
- Are perimeter firewalls installed between all wireless networks and the cardholder data environment, and are these firewalls configured to deny or, if traffic is necessary for business purposes, permit only authorized traffic between the wireless environment and the cardholder data environment?
- Is there a current network diagram that documents all connections between the cardholder data environment and other networks, including any wireless networks?
- Is there a formal process for approving and testing all network connections and changes to the firewall and router configurations?
These questions are difficult and often time-consuming to address. If you choose to work with a Clover POS system, you get to bypass most of them. The P2PE-certified hardware Clover builds includes multiple CPUs to protect data, even in the case of a virus being introduced to the system. Its high-level encryption protects customer information from the moment it is captured until it’s through the payment gateway. With this level of security built in, the PCI questionnaire merchants will have to complete is reduced to as few as five questions from 200+. And with add-ons like Clover Security, you can access a team of people who will help you across the finish line to PCI compliance!
In addition to your annual SAQ, you’ll also have to complete four system audits each year. If you are PCI compliant, these electronic audits will be a breeze. If you’ve cut a few corners thinking it will save you time or money, be prepared for an unnecessary headache.
If you use the services of Clover Security, you’ll get automated reminders to schedule and complete these audits as well as a guided questionnaire to complete your SAQ . That means you can spend more time running your business, and less time worrying about how to protect your payment data.